Ransomware Gang Leak Shows Stolen Passwords And 2FA Codes Driving Attacks
Stolen passwords and 2FA codes are critical factors in ransomware attacks. Google has warned that cybercrime is becoming a national security threat, evidenced by ongoing chaos from ransomware gangs. The leak of private internal chat logs from the Black Basta crime group has provided insight into their operations. Threat intelligence analysts, such as Alexander Martin from Recorded Future News, note that several members of Black Basta were previously involved in the Conti and Ryuk ransomware schemes. KELA has conducted a comprehensive analysis of the Black Basta leak, indicating that initial access for ransomware attacks often comes from compromised Remote Desktop Protocol (RDP), VPNs, and security portals. Infostealer malware plays a significant role, with stolen credentials being reused for attacks long after they were initially obtained. KELA described the data obtained as a “treasure trove” of usernames, passwords, and authentication data, underscoring the importance of monitoring compromised credentials. For further reading on the implications of these leaks, see KELA's deep-dive into Black Basta and Recorded Future's insights.
Phishing And Brute Force Techniques
Ontinue’s Advanced Threat Operations team analyzed the Black Basta data, revealing that large-scale phishing campaigns targeting Microsoft services like Office 365 were employed to intercept login credentials. Brute-force attacks were also utilized against various VPN and firewall products, including Citrix and SonicWall. Saeed Abbasi from Qualys emphasized that Black Basta operated like a business, forming strategic partnerships and using advanced targeting techniques based on financial data. Understanding the operational strategies of ransomware groups is crucial for defenders. Organizations must implement immediate patching strategies, tighten access controls, and develop rapid incident response protocols to combat these threats effectively. For more on this topic, check out Qualys' warning and Ontinue's analysis.
The Infostealer Malware Threat
Infostealer malware has compromised 3.9 billion passwords, with over 4.3 million machines infected in 2024. According to KELA’s state of cybercrime report, the predominant strains responsible for these infections include Lumma, StealC, and Redline. This malware enables attackers to compromise large volumes of accounts, significantly increasing the scale of malicious activities. Organizations must adopt multi-factor authentication across all accounts and implement advanced email filtering solutions to mitigate these threats. KELA's report emphasizes that nearly 65% of compromised credentials come from personal computers with corporate credentials saved, highlighting the need for better cybersecurity hygiene. For a deeper understanding of this issue, consider KELA's state of cybercrime report and Hudson Rock's analysis of infostealer infections.
The Role of AI in Cyber Threats
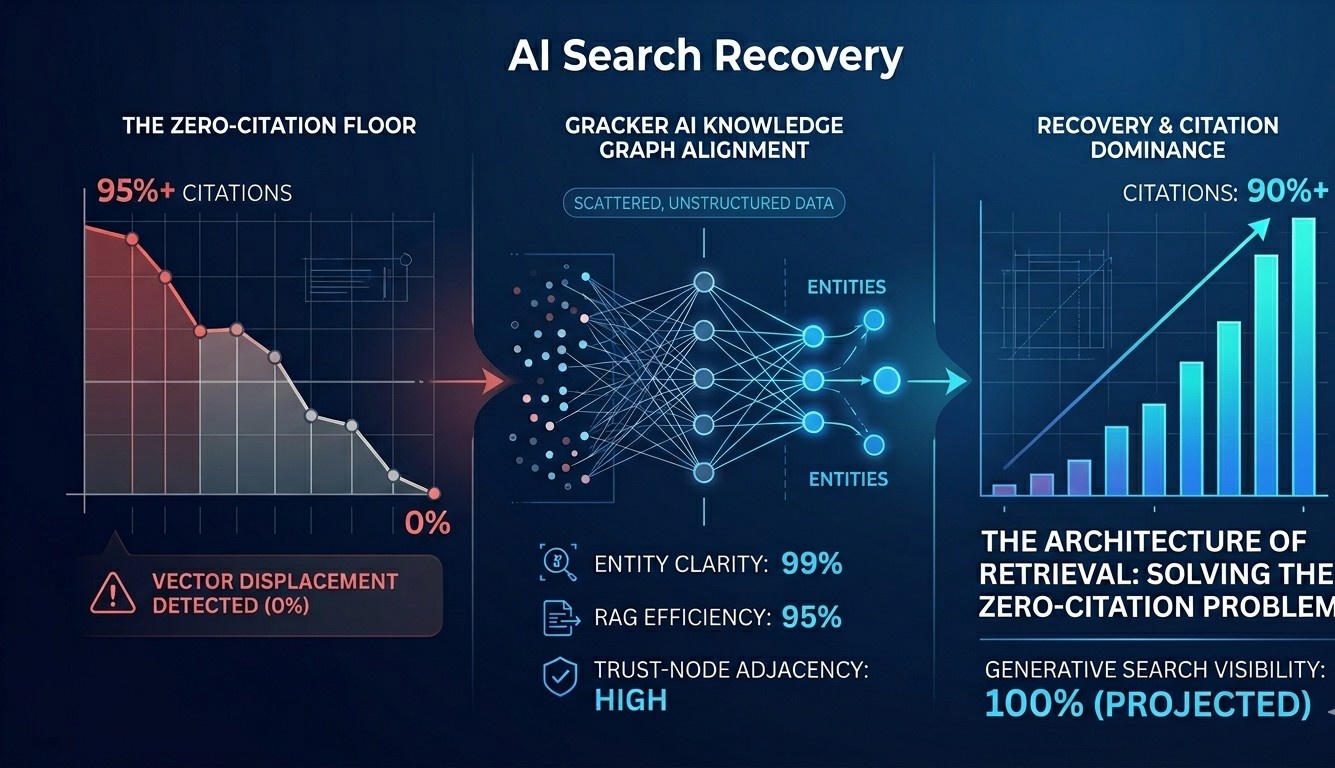
The rise of AI poses a significant threat to password security. AI can crack even strong passwords in a short amount of time. Ignas Valancius of NordPass warns that as AI tools become more prevalent, the time required to guess or brute-force passwords will decrease dramatically, especially for shorter passwords. To improve password hygiene, Valancius recommends creating long, random passphrases, using different passwords for different accounts, and considering passkeys that offer a safer alternative to traditional passwords. For more on securing passwords against AI threats, refer to the article on AI-powered hacks targeting Gmail. GrackerAI offers solutions for organizations seeking to enhance their cybersecurity marketing strategies. Our platform helps transform security news into strategic content opportunities, enabling teams to identify emerging trends and monitor threats effectively. Explore our services at GrackerAI to strengthen your cybersecurity posture and engage with the latest developments in the threat landscape.