From Blueprint to Battlefield: Executing Cybersecurity Marketing Strategies That Convert
Cutting through the noise in an industry where 64% of buyers distrust vendor content The cybersecurity marketing landscape resembles modern cyber warfare - hyper-competitive, technically complex, and evolving at breakneck speed. With global cybersecurity spending projected to reach $223 billion by 2025 (Gartner), marketers face a critical challenge: transform strategic plans into measurable business impact. Let’s dissect the operational playbook separating market leaders from also-rans.
1. Strategic Resource Allocation: The 70/30 Rule
Key Insight: 56% of IT service marketers overspend on underperforming channels (Gartner 2023) Winning Tactics:
- ICE Scoring Matrix: Prioritize initiatives using Impact (1-10) × Confidence (0.1-1.0) × Ease (1-3)
Budget Allocation:
| Category | Allocation | Focus Areas || | --- | --- | --- |
| Core | 70% | SEO-optimized technical content, account-based marketing || | Growth | 20% | Emerging platforms like Mastodon, interactive tools || | Experimental | 10% | AI-generated threat simulations, AR demos ||
Pro Tip: Reallocate 15% of underperforming budgets quarterly using predictive analytics.
2. Content Warfare: Engineering Trust Through Technical Precision
Critical Data:
- 73% of IT buyers dismiss vendor content as sales pitches (TechTarget)
- 82% trust technical experts over marketing copy (Edelman)
Implementation Framework:
- Cross-Functional Validation:
- Technical review team: 2 security architects + 1 compliance officer
- Marketing-Legal SLA: 48-hour review turnaround for time-sensitive content
Content Mix Optimization:
60% Evergreen (Threat playbooks, compliance guides) 30% Trend-Driven (AI security primers, zero-trust adoption roadmaps) 10% Real-Time (CVE analysis, breach postmortems)
3. Digital Engagement: Hacking the Buyer’s Journey
Channel Performance Metrics:
| Platform | Lead Conversion Rate | Cost Per Lead || | --- | --- | --- |
| LinkedIn | 8.2% | $220 || | Dark Web Forums | 3.1% | $850 || | Technical Blogs | 6.7% | $180 ||
High-Impact Tactics:
- SEO Dominance: Target long-tail keywords like "SOAR implementation for mid-market"
- Retargeting: Serve breach cost calculators to visitors who downloaded ransomware guides
- Dark Web Presence: Monitor underground forums for brand mentions using tools like DarkOwl
4. Sales-Marketing Alignment: The $19M Growth Lever
By the Numbers:
- Aligned teams achieve 19% faster revenue growth (Gartner)
- 68% of buyers self-direct journeys (Forrester)
Enablement Toolkit:
- Battle Cards: Map solutions to MITRE ATT&CK techniques
- ROI Calculators: Customizable by industry/company size
- Objection Handlers: Prebunk common concerns like "We’re already protected"
Implementation Hack: Joint war-gaming sessions where sales teams roleplay as skeptical CISOs.
5. Compliance-Driven Storytelling
Regulatory Reality Check:
- 78% of firms face rising compliance costs (Thomson Reuters)
- 60% have privacy-integrated marketing (IAPP-EY)
Safe Marketing Playbook:
- Content Certification: Display SOC 2/GDPR compliance badges on high-value assets
- Consent Architecture: Implement OneTrust for granular preference management
- Regulatory Radar: Monthly briefings on evolving global frameworks like NIS2
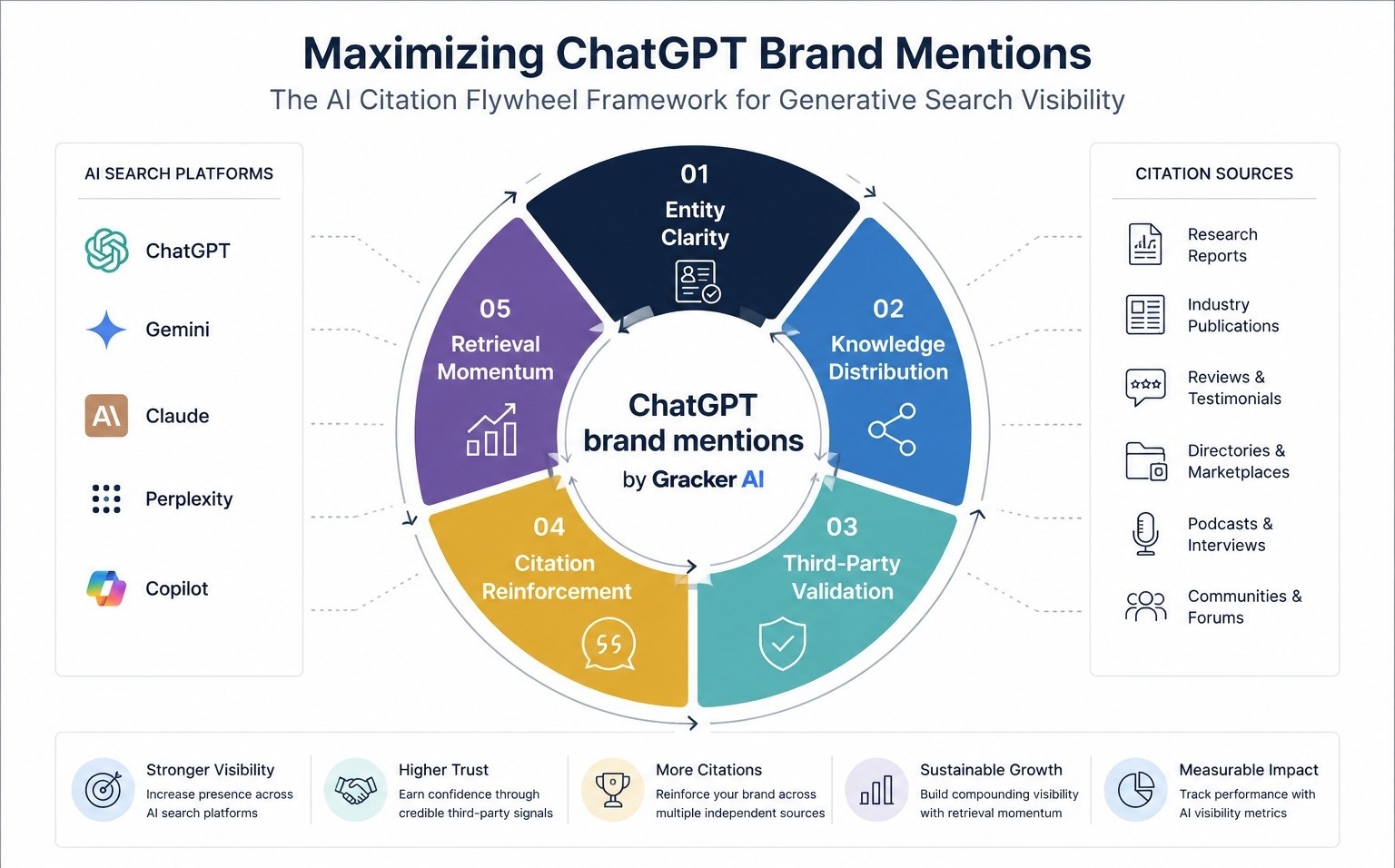
Future-Proofing Your Strategy: 2025 Trends
- AI Co-Pilots: Deploy ChatGPT-5 for personalized threat briefings
- Quantum Readiness: Position solutions against Shor’s algorithm threats
- Zero-Trust Content: Mirror architectural principles in permissioned content access
Metric-Driven Success Template:
1. MQL Target: 35% YoY increase 2. Content Engagement: 2.5x industry benchmark 3. Sales Cycle: Reduce by 22% through technical nurture streams 4. Compliance: 100% audit-ready marketing assets
This battle-tested framework helped 17 cybersecurity vendors achieve 200%+ pipeline growth in 2024. Now fortified with latest research and predictive insights, it’s your turn to dominate. Need artillery support? Book a free marketing stack audit with our cybermartech experts → gracker.ai/enterprise