System Intrusions Drive Majority of APAC Breaches
Verizon's 2025 Data Breach Investigations Report (DBIR) reveals that system intrusions are responsible for 80% of data breaches in the Asia-Pacific (APAC) region, marking a significant increase from 38% the previous year. The report analyzed over 22,000 security incidents, including 12,195 confirmed data breaches across 139 countries. Malware incidents rose steeply, now appearing in 83% of breaches, with ransomware present in 51%. 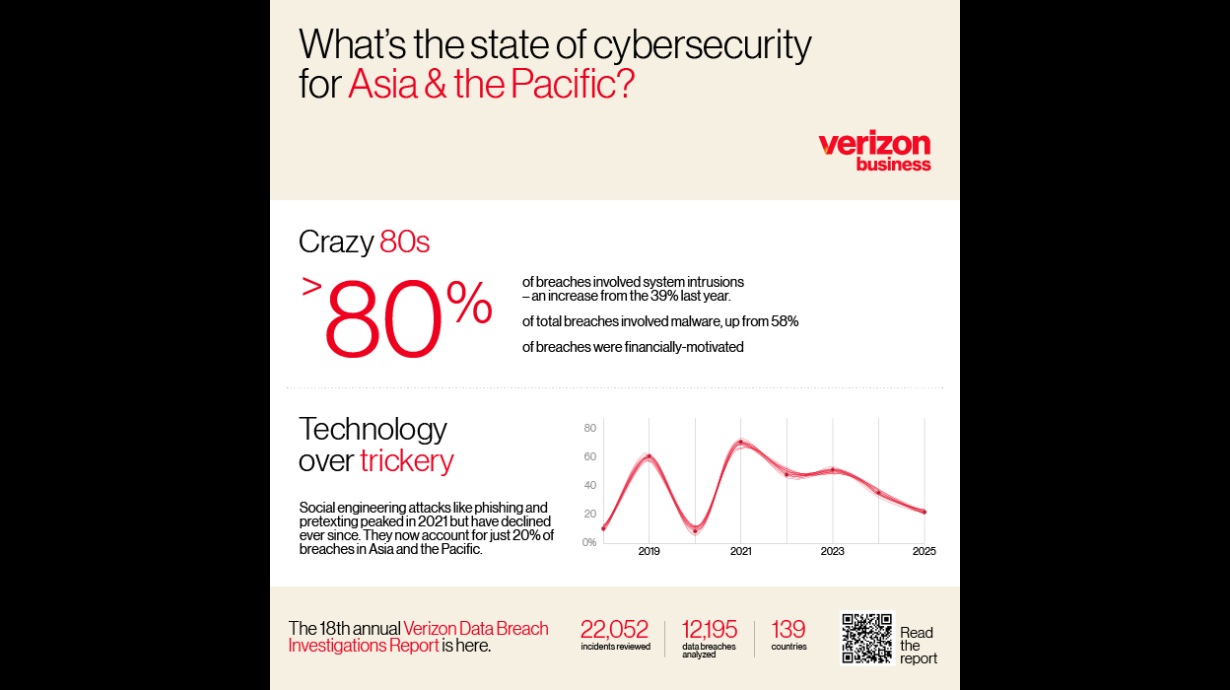
Key Findings in APAC
- Malware: The percentage of malware-related breaches increased from 58% to 83%, with email identified as the primary distribution vector.
- Ransomware: Ransomware now accounts for 51% of breaches, demonstrating a worrying trend where attackers publicly disclose breaches to exert pressure on victims.
- Social Engineering: Although social engineering breaches decreased, they still represent 20% of total breaches, attributed to the sharp rise in system intrusions.
For more on the trends in cybersecurity threats, check out the full report by Verizon.
Global Trends and Industry Insights
Globally, there has been a 34% increase in breaches resulting from the exploitation of vulnerabilities, particularly zero-day exploits targeting perimeter devices and VPNs. Ransomware incidents are present in 44% of global breaches, with the median ransom payment reported at $115,000. The involvement of third parties in breaches has doubled, indicating significant risks associated with supply chains and partner ecosystems. Human factors remain crucial, especially in contexts where social engineering overlaps with credential theft. Industries like Manufacturing and Healthcare have seen a rise in espionage-motivated attacks, while sectors such as Education, Financial Services, and Retail continue to be frequent targets. Small and medium-sized businesses (SMBs) are particularly vulnerable, with 88% of breaches affecting them involving ransomware. For a closer look at the implications of these trends, visit CNBC TV18.
Call for Enhanced Cybersecurity Measures
The findings of the 2025 DBIR serve as an urgent call to action for organizations to enhance their cybersecurity measures. GrackerAI, an AI-powered cybersecurity marketing platform, can help companies leverage these insights to create strategic content opportunities. By automating insights generation from industry developments, GrackerAI positions itself as a solution for creating timely, targeted marketing materials that resonate with cybersecurity professionals and decision-makers. For more information on how GrackerAI can assist your organization, explore our services or contact us at GrackerAI.
Latest Cybersecurity Trends & Breaking News
Rethinking Security in the AI Era Check Point Research AI Security Report Insights