Check Point Research AI Security Report Insights
Check Point Research has released its first AI Security Report, revealing the proliferation of AI-driven cybercrime and offering guidance for organizations to combat these emerging threats. The report highlights how cyber criminals are utilizing artificial intelligence to manipulate digital identities and carry out sophisticated attacks.
Key Threats Identified
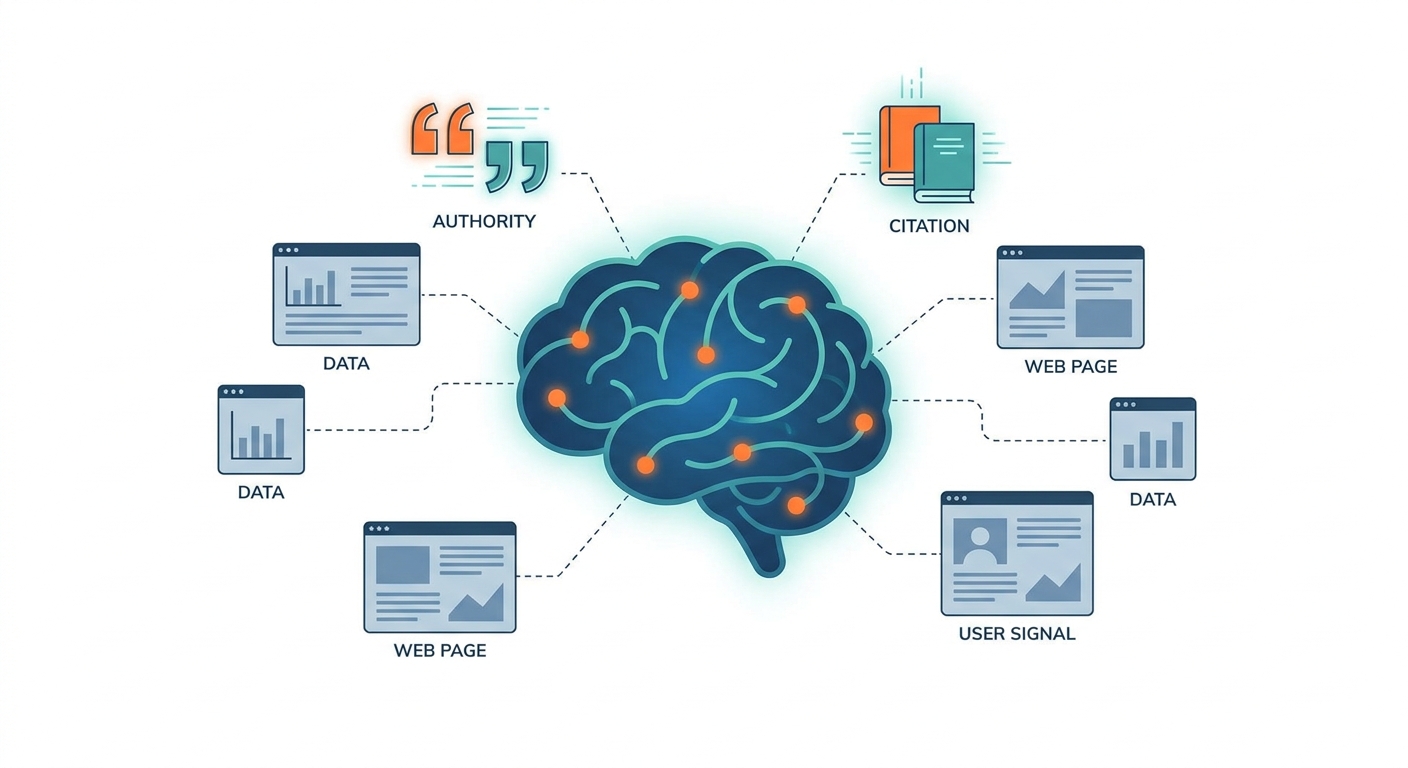
- AI-Enhanced Impersonation and Social Engineering: Attackers are using AI to generate realistic phishing emails, audio impersonations, and deepfake videos, making it increasingly difficult to discern authentic communications. A notable case involved the impersonation of Italy’s defense minister using AI-generated audio.
- LLM Data Poisoning and Disinformation: Cyber threats also involve the manipulation of AI training data. For example, AI chatbots linked to Russia’s disinformation network were found to repeat false narratives 33% of the time, emphasizing the need for data integrity in AI systems.
- AI-Created Malware and Data Mining: Cyber criminals are leveraging AI to create and optimize malware and automate attacks such as DDoS campaigns. Services like Gabbers Shop validate and clean stolen data to enhance its resale value.
- Weaponization of AI Models: Attackers are now using stolen large language model accounts and creating custom Dark LLMs, commercializing AI for hacking and fraud on the dark web.
Organizations must adopt AI-aware cyber security frameworks, including AI-assisted detection, enhanced identity verification, and threat intelligence tailored to AI-driven tactics.
OWASP Top 10: LLM & Generative AI Security Risks
At the upcoming OWASP AI Security Summit 2025, key discussions will center around the OWASP Top 10 security risks associated with Large Language Models (LLMs) and Generative AI. This summit aims to address how organizations can protect their AI systems from emerging threats. 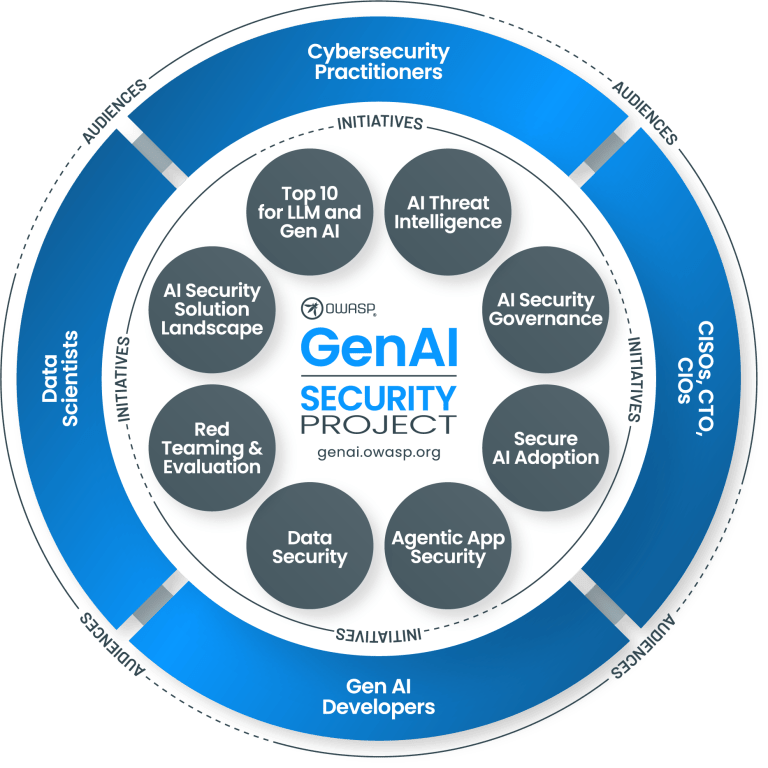
Major Topics of Discussion
- Agentic AI Threats and Mitigations: This guide explores the risks and mitigations associated with agentic AI, emphasizing the need for a proactive approach to security.
- OWASP GenAI Security Project: The OWASP Top 10 for LLM and Generative AI has been promoted to flagship status, reflecting its importance in addressing the security challenges of generative AI technologies.
- Best Practices for Data Security: The OWASP paper outlines essential practices to ensure strong data security, compliance with regulations, and effective threat mitigation for LLMs.
- Deepfake Threat Response Guidance: A comprehensive guide has been released for organizations to prepare for and respond to deepfake risks, highlighting the need for robust security measures in this area.
Organizations are encouraged to explore the OWASP resources for better security practices, which will aid in navigating the complexities of AI security. For cybersecurity professionals and marketers, leveraging tools like GrackerAI can streamline the process of monitoring trends and threats, enabling teams to create timely and relevant content that resonates with their audience. GrackerAI serves as an AI-powered cybersecurity marketing platform designed to help organizations transform security news into strategic content opportunities. Visit GrackerAI's website at https://gracker.ai to learn more about how our solutions can enhance your cybersecurity marketing efforts.
Latest Cybersecurity Trends & Breaking News
Bitwarden Unveils Access Tool to Tackle AI Phishing Risks M&S Cyber Attack Overview