The Essential Cybersecurity Content Strategy for Mid-Sized SaaS Companies in 2025

Most mid-sized SaaS companies know their security content needs an upgrade, but the path can look messy.
Threads, briefings, and buyer questions are scattered, and every sprint competes with writing time. A focused plan turns scattered inputs into assets people will trust, helping sales and customers feel safer.

Start With The Threats That Matter
Your buyers want clarity on real risks, not headlines. Frame your 2025 plan around availability, ransomware, and data exposure since they dominate the conversation.
Explain how your service resists disruption, contains malware spread, and protects tenant data without slowing product velocity.
State plainly which risks you do not cover, and how customers can mitigate them. Offer a roadmap snippet that shows what is coming next quarter. Transparency builds credibility and prevents overpromising during evaluations.
Map Content To The SaaS Customer Journey
Great security content meets buyers where they are. Create fast primers for top-of-funnel, practical guides for evaluation, and deeper patterns for implementation.
Pair each piece with the one question it answers so readers never wonder what to do next. Use short videos, annotated diagrams, and copy-paste snippets so busy readers can act quickly.
This is where your anchor play belongs. In a practical guide on incident readiness, explain triage, handoffs, and when to engage managed security operations so teams do not improvise under pressure. Close with a small worksheet that lists roles, contacts, and SLAs buyers can adapt.
Add a simple journey map so your team can see which assets support awareness, comparison, onboarding, and renewal. Revisit that map quarterly to retire stale pieces and plug gaps where buyers stall or bounce.
Treat each asset as a small promise: if it claims clarity, guarantee the steps are genuinely doable in under ten minutes.
Use real customer language pulled from tickets or sales notes so the content feels grounded, not theoretical. When every piece fits a stage and a job to be done, your library becomes a steady engine for trust and momentum.
Turn Research Into A Credible Narrative
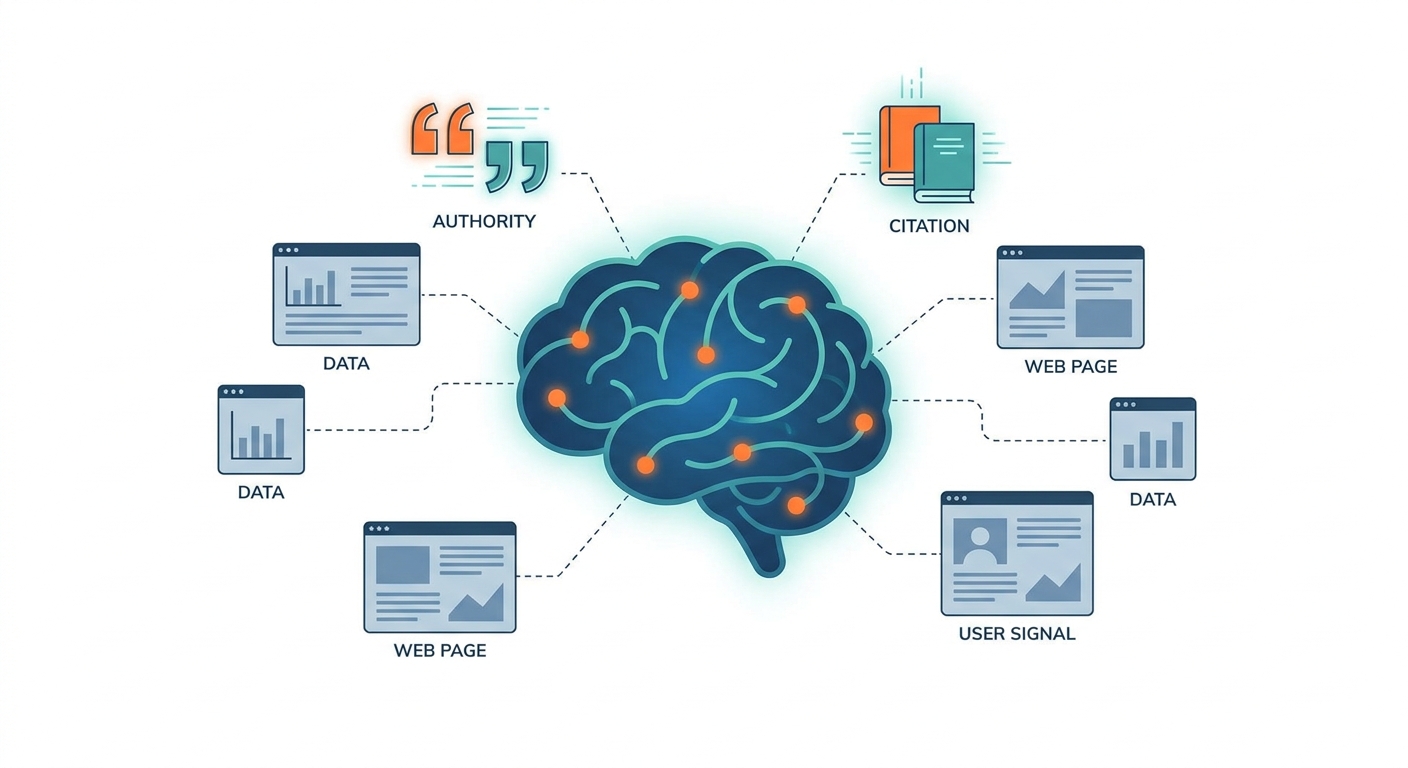
Security teams are inundated with reports, so curate a few authoritative signals and translate them into buyer language.
A recent European threat overview highlighted persistent pressure on availability and the rising profile of ransomware, which supports a content focus on resilience, recovery, and data safeguards.
Use short explainers that link threat trends to the exact controls your platform provides.
For every signal, include an example scenario, the control that mitigates it, and the metric that proves it worked. Keep each block to three sentences. Visuals beat adjectives, so favor tables over fluff.
Cover Shadow IT And AI App Sprawl
Many mid-market teams rely on dozens of sanctioned SaaS apps plus a long tail of unsanctioned ones.
Industry research recently noted that fewer than half of organizations prioritize securing all sanctioned apps, and only a small minority extend that priority to unsanctioned apps.
Your content should show how to discover, classify, and govern both categories without slowing teams down.
Publish a quarterly app census template
Provide a data classification quicksheet
Offer guidance for OAuth risk reviews
Share a checklist for admin offboarding
Include a sample approval workflow
Build A Reusable Content System
Treat security content like a product that ships on cadence. Run a monthly editorial meeting with PM, security, and sales engineering. Lock a reusable outline for briefs, playbooks, and post-incident reports so contributors never start from scratch.
Define owners for facts like encryption defaults, backup intervals, and isolation boundaries. Store source-of-truth snippets in a shared doc so updates flow into every asset. Add a short peer review to catch stale screenshots, ambiguous claims, and jargon.
Prove Trust With Evidence And Cadence
Trust grows when you ship small, useful updates on a predictable rhythm. Publish change logs for security features, quarterly notes from your risk committee, and clear summaries of tabletop exercises.
Show how often you test backups, what your recovery targets are, and how you validate tenant isolation at scale. Add date stamps on diagrams and include version histories so buyers see forward motion, not static promises.

Measure What Moves Deals Forward
Track which assets shorten sales cycles or reduce security questionnaires.
Useful metrics include time-to-first-meaningful-answer for security pages, the number of questionnaire items satisfied by public docs, and the ratio of follow-up questions per opportunity. If an asset does not change behavior, rewrite it.
Create a simple scorecard that evaluates clarity, accuracy, and buyer relevance. Ask sales and support to rate content after calls and tickets, then fold that feedback into the next sprint. Over time, the library becomes sharper and easier to maintain.
Strong security content is not about louder claims. It is about teaching buyers how to evaluate you, proving you run a disciplined program, and showing progress every quarter.
With a focused plan and steady cadence, your 2025 strategy will help customers understand your posture and help your team win deals with less friction. Write for clarity first, then depth, and always tie guidance to real operational practice.